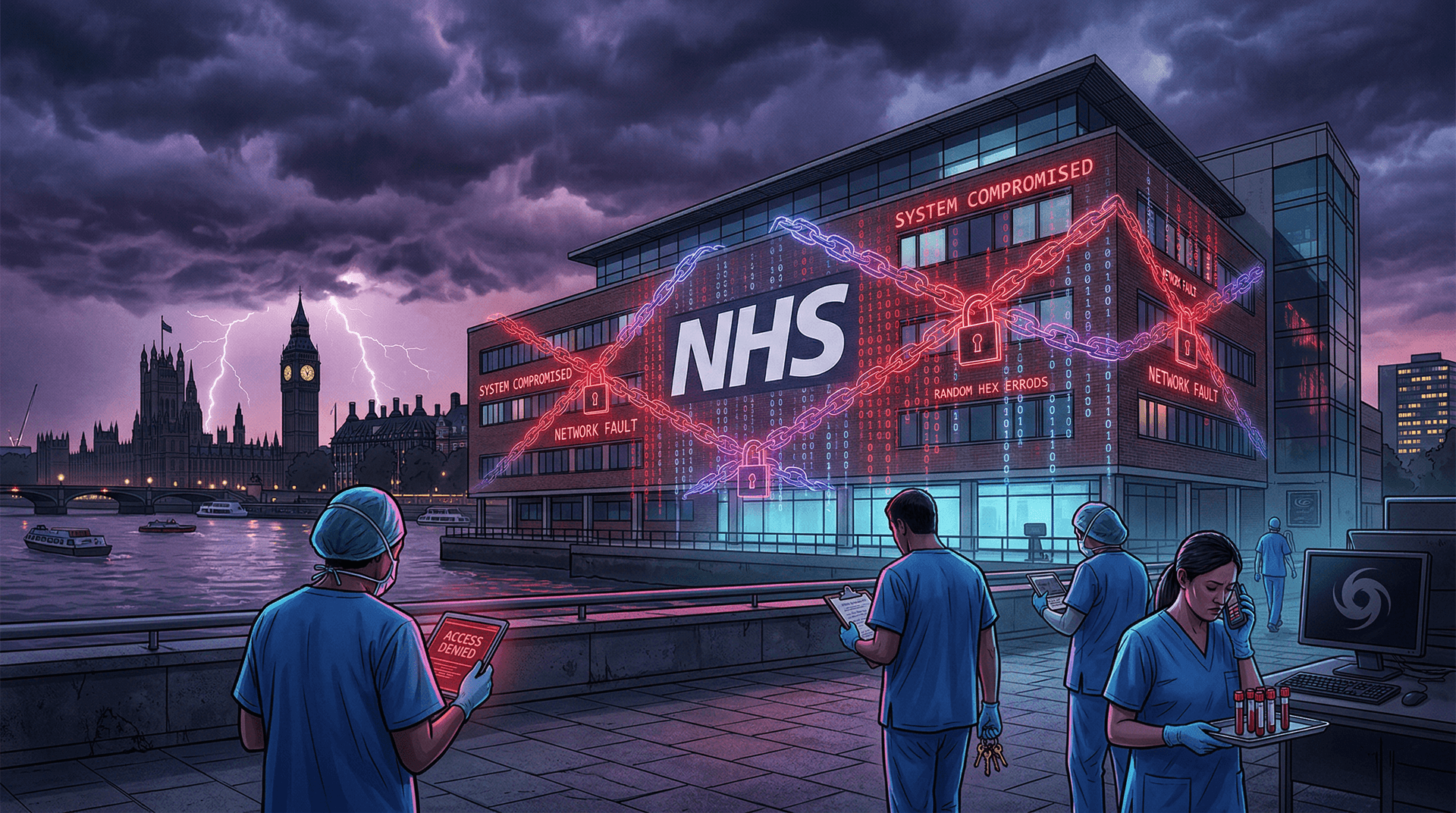
In a stark reminder of the fragility of critical healthcare infrastructure, the ransomware group Qilin launched a devastating attack on Synnovis—a pathology services provider for two of London's largest NHS hospital trusts—on June 3, 2024. The breach forced the postponement of thousands of outpatient appointments, urgent blood tests, and even impacted blood transfusion services, underscoring the escalating threat of cyberattacks on public health systems.
The Attack Unfolds
Synnovis, which handles blood testing and diagnostics for King's College Hospital NHS Foundation Trust and Guy's and St Thomas' NHS Foundation Trust, confirmed the cyber incident early Monday morning. By midday, the company acknowledged that its IT systems were compromised, leading to widespread disruptions. The Qilin group, known for its aggressive tactics, quickly claimed responsibility on its dark web leak site, posting samples of allegedly stolen data to pressure the victim into paying a ransom.
The immediate fallout was severe. Over 1,600 outpatient appointments were canceled on the first day alone, with an additional 200 urgent blood tests postponed. Pathology services, essential for diagnosing conditions from cancer to infections, ground to a halt. Hospitals resorted to manual processes where possible, but the scale of the disruption meant patients faced delays in critical care. Blood stocks dwindled as testing capabilities faltered, prompting urgent appeals for donations.
NHS England described the situation as 'extremely challenging,' with clinicians working around the clock to prioritize life-saving procedures. Emergency services remained operational, but elective surgeries and routine diagnostics were hit hardest.
Who is Qilin?
Qilin, also tracked as Agenda by some cybersecurity firms, emerged in mid-2022 as a Russian-speaking ransomware-as-a-service (RaaS) operation. The group has a track record of targeting high-value sectors like healthcare, finance, and government. Notable victims include Anglo American (a mining giant) and several US healthcare providers. Qilin's modus operandi involves double extortion: encrypting data for ransom and threatening to leak exfiltrated information.
According to a recent report from cybersecurity firm Group-IB, Qilin has extorted over $50 million since its inception, with healthcare comprising about 15% of its attacks. The group favors Linux-based encryptors and employs custom tools to evade detection, often exploiting unpatched vulnerabilities in VPNs or remote access tools.
In the Synnovis case, initial investigations point to a phishing campaign or compromised credentials as the entry point, though details remain under wraps as the National Cyber Security Centre (NCSC) and National Crime Agency (NCA) lead the probe.
Broader Impacts on the NHS
This is not the NHS's first brush with ransomware. The health service has faced a barrage of attacks, including the 2017 WannaCry outbreak that paralyzed hospitals across the UK and the 2022 Irish HSE ransomware incident. In 2023 alone, the NHS reported over 1,500 cybersecurity incidents, with ransomware accounting for 20%.
The Synnovis attack exacerbates existing pressures: chronic understaffing, post-pandemic backlogs, and aging IT systems. Pathologists are now manually processing samples, a labor-intensive process that could take weeks to clear. Patient safety remains the priority, but the human cost is mounting—cancer screenings delayed, transplant patients waiting, and routine care deferred.
Economically, the hit is substantial. Synnovis serves over 40% of London's pathology needs, processing 25 million tests annually. Downtime translates to millions in lost productivity and recovery costs, not to mention reputational damage.
Response and Recovery Efforts
Synnovis disconnected affected systems to contain the spread, activating incident response plans in coordination with NHS Digital and the NCSC. Forensic experts from Mandiant and CrowdStrike have been rumored to be on-site, though not officially confirmed.
No ransom payment has been made or demanded publicly beyond the leak site taunts. UK policy, aligned with US guidance, strongly discourages payments to cybercriminals, as they fund further attacks. Recovery hinges on backups—Synnovis claims robust offsite data, but restoring petabytes of pathology records is no small feat.
The government has pledged support, with Health Secretary Victoria Atkins addressing Parliament on June 4. 'This is an outrageous assault on our NHS,' she stated, promising bolstered cyber defenses.
Lessons for Healthcare Cybersecurity
Healthcare's allure for attackers is clear: sensitive data fetches high prices on dark markets (a single medical record can sell for $1,000+), and disruptions cause real-world harm, pressuring victims to pay. The sector lags in cybersecurity maturity—many trusts run legacy systems incompatible with modern defenses.
Experts like Kevin Beaumont, former NCSC advisor, warn: 'NHS IT is a patchwork quilt of outdated tech. Multi-factor authentication (MFA) everywhere, zero-trust architectures, and regular pen-testing are non-negotiable.'
Global stats paint a grim picture. IBM's 2024 X-Force report notes healthcare breach costs averaged $10.93 million, highest of any industry. Ransomware surged 20% year-over-year, with 67% of attacks unpatched vulnerabilities.
Recommendations post-Synnovis:
- Patch Management: Prioritize critical flaws like those in Citrix or Log4j.
- Endpoint Detection: Deploy EDR tools like Microsoft Defender or SentinelOne.
- Training: 95% of breaches involve human error; phishing simulations save lives.
- Incident Response: Annual tabletop exercises with external partners.
- Supply Chain Security: Vet third-parties like Synnovis rigorously.
Looking Ahead
As of June 5, partial services are resuming, but full recovery may take weeks. This attack spotlights the need for national investment— the UK's £2.6 billion cyber strategy must prioritize health.
Internationally, it echoes US incidents like the Change Healthcare breach earlier in 2024, affecting one-third of Americans. Collaboration via forums like the Health-ISAC is vital.
The Qilin saga continues; expect more leaks if no ransom is paid. For now, London's patients bear the brunt, a poignant symbol of cyberwar's frontline shifting to hospital wards.
Word count: 912